Simplify Cybersecurity Documentation.
Pass Audits. Meet Mandates. Prove Maturity.
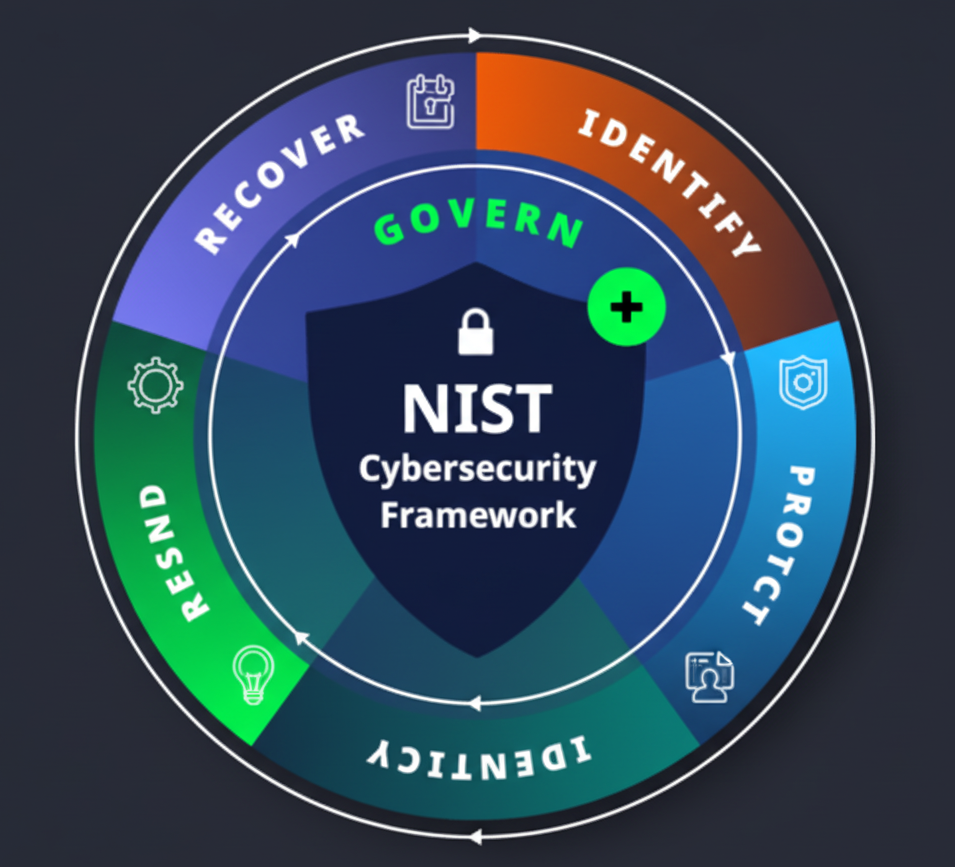
Fully customizable cybersecurity templates mapped to NIST CSF 2.0 so you can launch or level-up your security program fast.
Built by assessors. Structured for auditors. Designed for real-world adoption.
How it works
Four simple steps to clear documentation and faster audits.
Pick your Bundle
Start with a bundle for compliance documentation needs.
Download your templates
Every document maps to NIST CSF 2.0
Customize
Edit placeholders, add roles/owners, and align to your environment.
Review and Implement
Review each document and track each Exception.
Aligned with NIST CSF 2.0
Show your maturity with built-in control mappings. Each policy and plan includes a regulation map so reviewers can trace coverage quickly.
- • Policy → CSF Function/Category/Subcategory
- • Evidence references and responsibilities
- • Ready for cybersecurity assessments and insurance questionnaires
Policies, Procedures, Plans, and Templates
Get started with our most downloaded policies, procedures, and plans.
Full Documentation Bundle
Equivalent consulting documentation value: $15,000+
$999
A complete compliance documentation package. Get every policy, plan, and procedure you need in one complete bundle — no piecing things together. Perfect for local governments and organizations of all sizes ready to show maturity, meet multiple regulations, and walk into audits with confidence.
- 38 - Information Security Policies and Procedures
- Each Policy Mapped to NIST CSF 2.0
- Policies and Procedures Exception Tracking Template
- Policies and Procedures Regulation Map
- Incident Response Plan & Implementation Guide
- Contingency Disaster Recovery Plan & Implementation Guide
- Business Impact Analysis Template
- Disaster Recovery & Incident Response Runbook Templates
Information Security Policy & Procedure Bundle
A comprehensive foundation to protect your digital assets.
$299
The smart starting point for building cybersecurity maturity. This bundle delivers 38 core security policies mapped to NIST CSF 2.0 — plus an exception tracking template and regulation map — giving you the structure you need from day one. Perfect for local governments, businesses, and organizations that want clear governance without the guesswork.
- 38 - Information Security Policies and Procedures
- Each Policy Mapped to NIST CSF 2.0
- Policies and Procedures Implementation Guide
- Policies and Procedures Exception Tracking Template
- Policies and Procedures Regulation Map
Incident Response Documentation Bundle
Be ready to respond when incidents strike.
$299
Everything you need to respond quickly and effectively to cyber threats. This bundle includes a full incident response policy, implementation guide, response plan, and runbook template — giving your team a clear playbook for action. Perfect for local governments, businesses, and organizations preparing for ransomware, phishing, or any incident scenario.
- Incident Response Policy and Procedure
- Incident Response Implementation Guide
- Incident Response Plan
- Incident Response Runbook Template
Contingency & Disaster Recovery Documentation Bundle
Prepare, respond, and recover with confidence.
$399
Be ready for outages, disasters, and unexpected downtime. This bundle includes recovery policies, implementation guides, and planning tools — including a Business Impact Analysis — to keep your operations resilient. Perfect for local governments, businesses, and organizations that need to demonstrate resilience to clients, regulators, and insurers.
- Contingency Disaster Recovery Policy and Procedure
- Contingency Disaster Recovery Implementation Guide
- Contingency Disaster Recovery Plan
- Business Impact Analysis Template
- Disaster Recovery Runbook Template
Education, Training, Implementation, and Assessments
Coming Soon!
For organizations that want hands-on help. Expert-led training ensures your team not only has the documents, but knows how to use them effectively. Great for building confidence, improving adoption, and making compliance “stick.”
Join the WaitlistIs your Password Policy Audit-Ready?
Use our free NIST 800-63B assessment to bridge the gap between your password policy and audit requirements.
- • Visual Risk Mapping: Generate an instant Radar/Spider chart to identify password "blind spots."
- • Maturity Scoring: Receive a weighted maturity score based on NIST 800-63B standards.
- • Prioritized Remediation: Get an auto-generated list of "Immediate" fixes for your highest risks.

Higher coverage area indicates stronger password control maturity.
Targeted Compliance Solutions
Documentation frameworks tailored for your industry’s unique regulatory demands.
Business & Enterprise
Establish a rock-solid security baseline that protects your reputation and speeds up insurance applications.
- ✔ NIST CSF 2.0-aligned security baseline.
- ✔ Clear guidelines to reduce human error.
- ✔ Governance evidence for partners and insurers.
Public Sector, Education & Healthcare
Built for municipalities, school districts, and healthcare industries. Documentation that meets state-level mandates and regulatory oversight.
- ✔ IR, Disaster Recovery, and BIA tools.
- ✔ Ownership defined for public entity roles.
- ✔ Audit-friendly for state/local assessments.
About Us
RiskDocx was built by cybersecurity professionals who have spent decades inside real-world assessments, audits, and incident response engagements. We understand what regulators, insurers, and examiners look for—because we’ve sat across the table from them.
We created RiskDocx to eliminate the guesswork from cybersecurity documentation. Our templates are structured, mapped to NIST CSF 2.0, and designed to help organizations demonstrate maturity—not just create paperwork.
Today, we support commercial enterprises, public sector organizations, and healthcare providers who want clear governance, defensible documentation, and confidence walking into assessments.
It all starts with Policy
Organizations across sectors face escalating cybersecurity threats and growing regulatory pressure. The data tells the story. Policies provide the essential framework that transforms chaotic individual actions into a unified defense, ensuring every employee knows how to handle data and respond to threats. Without these documented standards, an organization remains legally vulnerable and technically inconsistent, leaving the door open for human error to bypass even the most expensive security tools.
Healthcare
Experienced a breach in the past two years
Average breach cost per patient record
Incidents involved ransomware
Public Sector
Governments targeted by ransomware
Average operational downtime post-attack
Recovery and restoration costs
Commercial
Average global cost of a data breach
Breaches involving human error
YOY increase in ransomware incidents
Source: IBM Cost of a Data Breach Report
Trusted by Professionals
"With new Cybersecurity mandates, the RiskDocx templates helped us get our documentation in order."
Business Manager, Jackson Township
"RiskDocx helped us prepare for an assessment in days, not weeks. The clarity and customization were a game-changer."
CISO, Community Health
"Finally, a tool that takes the headache out of cybersecurity policy generation. Highly recommend for any organization."
Security Consultant, SecureNow Inc.
Get a Free Social Media Policy
Fully editable and mapped to NIST CSF 2.0. We’ll email the download and a short tips series.
No spam. Unsubscribe anytime.
FAQs
Quick answers about templates, formats, and mapping.
What file formats do you provide? ⌄
All our templates are provided in Microsoft Word (.docx) format for easy editing and customization. They are compatible with MS Word, Google Docs, and other major word processors.
How is NIST CSF mapping shown? ⌄
Each policy or plan contains a mapping table to Functions/Categories/Subcategories and a regulation map to speed audits.
Is this legal advice? ⌄
No. RiskDocx is not a law firm, and our templates do not constitute legal advice. They are a starting point for your documentation. We strongly recommend you consult with a qualified legal professional to ensure your final documents comply with all applicable laws and regulations for your specific situation.
Are these documents all I need for compliance? ⌄
No. The documents are a foundation, but compliance requires more than just having policies on paper. You need to adopt and implement the processes outlined in each document, ensure your workforce is trained, and actively track exceptions or deviations. Compliance is an ongoing program of execution, monitoring, and improvement—not a one-time purchase.